Two Microsoft Exchange Zero-Days Exploited by Attackers (CVE-2022-41040, CVE-2022-41082)
According to Microsoft, two new Exchange zero day vulnerabilities in Exchange are under active attack, but there are no immediate fixes
Microsoft has confirmed that two unpatched, zero-day vulnerabilities in Exchange Server are being exploited by cybercriminals in real-world attacks. And they investigating reports that attackers are exploiting two previously unknown vulnerabilities in Exchange Server, a technology many businesses rely on to send and receive email. Microsoft says it’s speeding up work on software patches to close security vulnerabilities. Meanwhile, it’s urging a subset of Exchange customers to enable a setting that could help mitigate ongoing attacks.

Microsoft’s Security Response Center (MRSC) said in a blog post on Thursday that the two vulnerabilities were identified as CVE-2022-41040, a server-side request forgery (SSRF) vulnerability, while the second was identified as CVE-2022-41082 . Allows remote code execution on a vulnerable server when PowerShell is accessible to the attacker.
About the Exchange Vulnerabilities (CVE-2022-41040, CVE-2022-41082)
CVE-2022-41040 is a Server-Side Request Forgery (SSRF) vulnerability, and CVE-2022-41082 allows remote code execution when PowerShell is exposed to the attacker, Microsoft explained.
“At this time, Microsoft is aware of limited targeted attacks using the two vulnerabilities to get into users’ systems. In these attacks, CVE-2022-41040 can enable an authenticated attacker to remotely trigger CVE-2022-41082. It should be noted that authenticated access to the vulnerable Exchange Server is necessary to successfully exploit either of the two vulnerabilities.”
The vulnerabilities affect Microsoft Exchange Server versions 2013, 2016 and 2019.
Unfortunately, although Vietnamese researchers informed Microsoft (via Trend Micro’s Zero Day Initiative) about the bugs a few weeks ago, there are still no patches.
GTSC researchers initially thought the attackers were exploiting the ProxyShell vulnerability, but further analysis showed that the affected MS Exchange servers were up to date with the patches, so the ProxyShell exploitation theory was rejected.
According to security researcher Kevin Beaumont, the ProxyShell patches from early 2021 don’t seem to have solved the problem. “I am calling this ProxyNotShell, as it is the same path and SSRF/RCE pair from back then… but with authentication.”
Mitigation and Detection of Exchange Zero Day Vulnarability
GTSC researchers discovered the attacks in early August and said the attackers’ ultimate goal was to “create backdoors on the affected system and cross-walk to other servers in the system.”
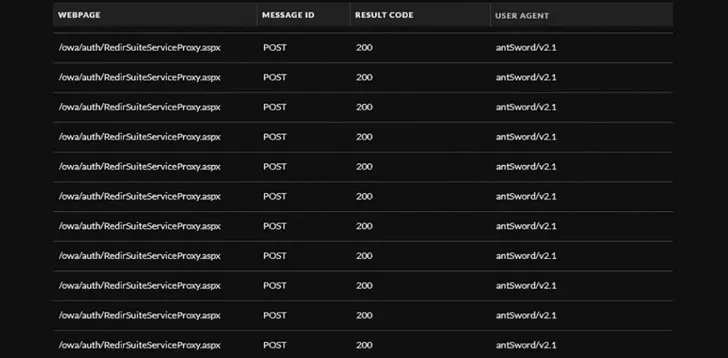
The first was done by releasing webshell. “Using the user-agent, we determined that the attacker uses Antsword, an active, open-source, cross-platform Chinese-language website administration tool that helps manage web shells,” they said.
GTSC has provided indicators of compromise and guidelines, as well as a tool that defenders can use to search IIS log files for evidence of compromise.
Both Microsoft and Trend Micro have provided detection queries and explained how to use their investigation and repair solutions.
“A quick sweep of the internet suggests a lot of organisations haven’t yet patched for ProxyShell, which is understandable given how Exchange patching works,” Beaumont noted and determined (via Shodan) that there are nearly 250,000 vulnerable Exchange servers available on the Internet.
Previous Attack – Exchange Zero Day Vulnarability
In March 2021, hundreds of thousands of organizations around the world had their email stolen and multiple backdoor webshells installed, that is fourth exchange server zero day vulnerability.
Granted, the zero-day bugs that fueled this debacle were far more critical than the two detailed this week, and there’s still no sign that the exploit code has been publicly released (which is likely to be soon will change). But part of what made last year’s mass Exchange Server hacks so pervasive was the fact that vulnerable organizations received little or no warning of what to look for before fully hacking their Exchange Server environments were owned by more attackers.
Microsoft is quick to point out that these zero-day flaws require an attacker to have a valid username and password for an Exchange user, but that may not be such a daunting task for the hackers behind these latest exploits against Exchange Server .
Findings -Latest Exchange 0 Day Vulnarability
Security researchers are warning of previously undisclosed bugs in fully patched Microsoft Exchange servers that malicious actors are exploiting in real-world attacks to achieve remote code execution on affected systems.
That’s according to Vietnamese cybersecurity firm GTSC, which discovered the flaws as part of its security monitoring and incident response efforts in August 2022.
The two vulnerabilities that have yet to be formally assign CVE identifiers are identified by the Zero Day Initiative as ZDI-CAN-18333 (CVSS Score: 8.8) and ZDI-CAN-18802 (CVSS Score: 6.3) tracked.
GTSC said successful exploitation of the vulnerabilities could be exploited to gain a foothold in victim’s systems, allowing attackers to drop web shells and perform lateral movements over the compromised network.
“We found that web shells, mostly obfuscated, were being placed on Exchange servers,” the company noted. “By using the user-agent, we determined that the attacker uses Antsword, an active Chinese-based open-source cross-platform website administration tool that supports web shell management.”
Exploitation requests in IIS logs are said to appear in the same format as the ProxyShell Exchange Server vulnerabilities, with GTSC noting that the target servers have already been patched against the flaws disclosed in April 2021.
The cybersecurity company theorized that since the web shell is coded in Simplified Chinese (Windows code page 936), the attacks likely came from a Chinese hacking group.
The attacks also employ the China Chopper web shell, a lightweight backdoor that can grant persistent remote access and allow attackers to reconnect at any time for further attacks.
So What in Conclusion
- We can say with certainty that attacks on Exchange servers have taken place that match these patterns
- We can’t say for sure it’s zero-day with the information provided – it looks more like ProxyShell to me. UPDATE: Forget that, Microsoft says there are two new zero days.
- The information provided may not be complete or there may be a patch regression somewhere
- Microsoft, ZDI and GTSC need to talk to each other
- Some of the injected malware (the back door) appears to be brand new
- As always, keep calm and carry on.
Also Read: WhatsApp Zero Day Vulnarability


