Meltdown and Spectre Bugs that Exploit CPU Vulnerabilities
The latest finding from a team of researchers has revealed weaknesses in Intel processor chips. It affects every home and workplace using any of the Mac, Linux or Windows operating system. They have discovered that the CPUs made in the last two decades have Meltdown and Spectre vulnerabilities. This Massive Meltdown Attack & Spectre Bug This Massive Meltdown Attack & Spectre Bug has affected the majority of Computer chips across the world. These are new finding and a lot is not known about it. It impacts every system designed by any manufacturer since 1995 and even virtual ones. This post mentions all there is to know about this issue. It explains in detail what causes these problems in a computer and how to fix it. Read all about it in the following segment.

What is Meltdown and Spectre Attack?
There are shortcomings in any modern day technology including processors. Some malicious entities take advantage of this weakness to gain access to unauthorized private information, passwords etc. It can leave a user susceptible to possible attack at any moment.
Meltdown and Spectre bugs exploit vulnerable computers by gaining access to it. This can be done by a JavaScript code which can easily override the existing operating system. It can map the kernel and gain access to secure company data. This program can be maliciously installed without the knowledge of the user. It can come with running an application from an unknown source.
Meltdown and Spectre steal data that is currently being processed on the computer. An operating system usually does not allow another application to read data from a running program. The Meltdown and Spectre bugs bypass this security feature to get hold of secrets in the memory of these programs. This includes saved passwords on a browser, personal chats, secret email conversation, private photos, and crucial business documents etc.
What is Meltdown?

Meltdown breaks into the security between operating system & user application. It leverages a flaw in out-of-order execution to make changes in CPU cache state. The Meltdown attack uses this isolated data to hack into personal information. It is potentially quite lethal as this can even affect virtual machine to target host system. One can buy space of hosting cloud service to access server data. If successful, the entire kernel address space with physical memory can be copied. This means all the data saved on a computer.
What is Spectre?

Spectre is a bug that exploits processor flaws and tricks an application into revealing information stored in its memory. This can affect any system with Intel, AMD or ARM chips.
How to Resolve Meltdown and Spectre Vulnerabilities?
All the leading companies like Microsoft, Google, Apple have been informed it. They have released the latest patch that can help with this situation. Users are advised to download the latest updates offered by the Windows, Mac or Linux computer.
FAQs related to Meltdown and Spectre Attack
Ques: Who is affected by this Meltdown and Spectre bugs?
Ans: Everyone who has a computer since 1995.
Ques: Can the Antivirus detect this attack?
Ans: Yes, many companies have already sent out patches. It identifies this flaw and notifies the user of the same.
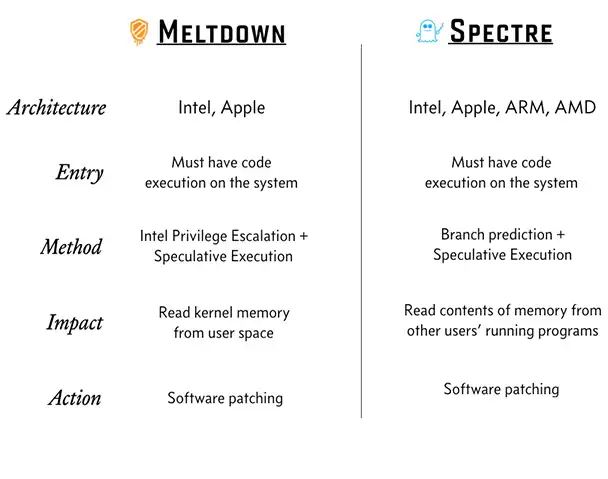
Ques: What is the difference between Meltdown and Spectre?
Ans: Meltdown breaks down the process where applications have cache memory which is not being used. The program can be running and using system memory at the same time. Meanwhile, Spectre tricks program in accessing part of memory where private information is saved. It copies the data for personal gain by a malicious attacker. Both use flaws already present in a processor in creative ways but are completely different.
Conclusion
Both these vulnerabilities have surfaced recently does not impact any more than a random virus. One can gather all the information about it through this post. It covers most of the reasons for Meltdown and Spectre vulnerabilities. It can be used as a source of useful information to share with peers and inform others. Every IT department must be updated about the latest in the field of data security and this is one. Make sure to keep the system updated to avoid anything bad happen on a personal computer.


